Tag: Google Cloud
-
Hands-on learning Cloud Technologies with QwikLabs
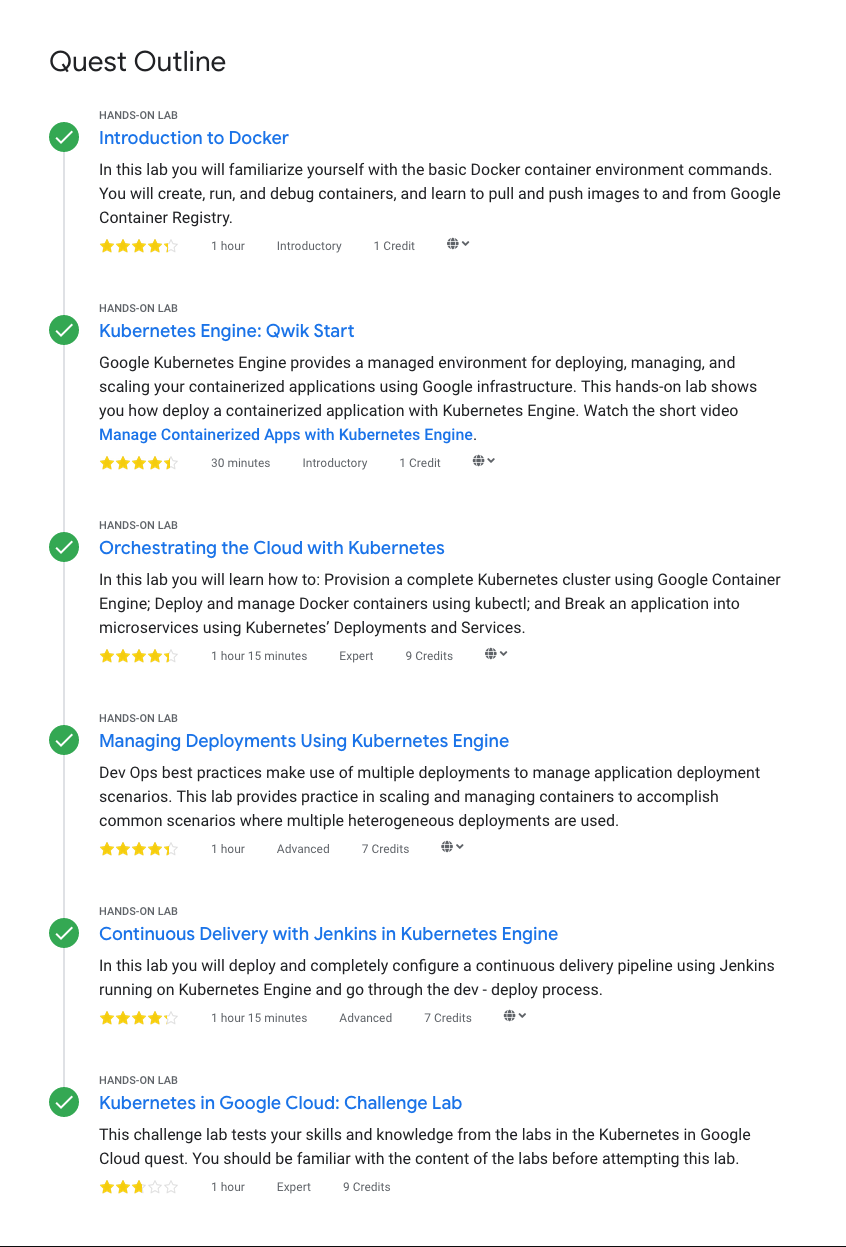
I’ve used Google Cloud Platform for some time and got a opportunity to attend Codemen Cloud Academy’s Google Workshop which concentrated to “Kubernetes in the Google Cloud” and “Google Cloud Run Serverless Workshop” topics using the Qwiklabs is a platform. Here’s my (very) short notes from the workshop and using Qwiklabs.… Jatka lukemista →
-
Using NGINX Ingress Controller on Google Kubernetes Engine
If you’ve used Kubernetes you might have come across Ingress which manages external access to services in a cluster, typically HTTP. When running with GKE the “default” is GLBC which is a “load balancer controller that manages external loadbalancers configured through the Kubernetes Ingress API”. It’s easy to use but doesn’t let you to to…