What is DevSec, how to use Docker securely, why developers leak credentials? All those questions were answered at OWASP Helsinki chapter meeting #31 which was held 13.6.2017 at Solita premises. Here’s my short notes from the event. I’ll add links to presentations when they’re available.
DevSec – Developers are the key to security
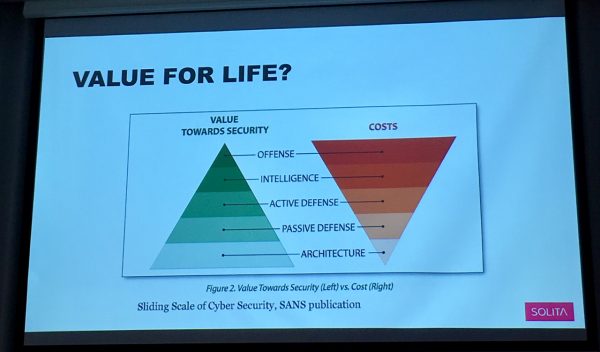
DevSec is a emerging trend to move developers closer to security experts, akin to DevOps. Antti Virtanen from Solita talked about DevSec and how they do it (slides, pdf). As talk’s title tells us developers are the key but often buying one cybersolution is easier (giving out money) than peoples’ time. But if we look at the return of investment, passive defense is more effective.
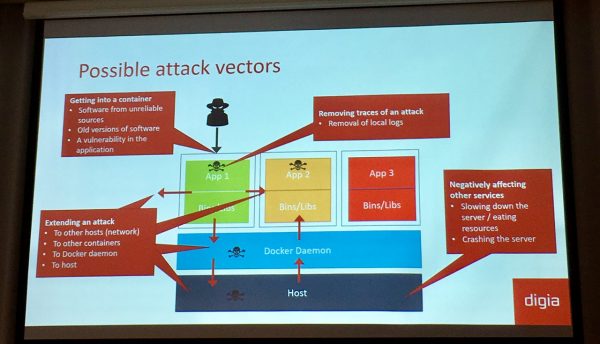
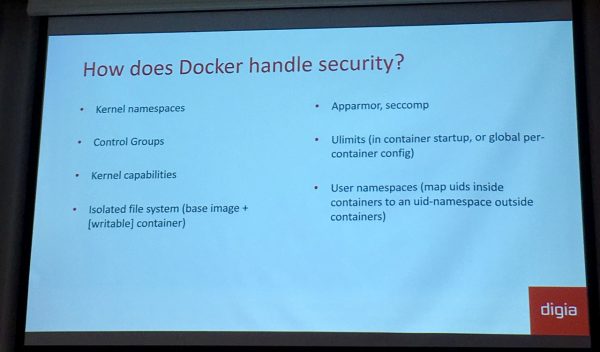
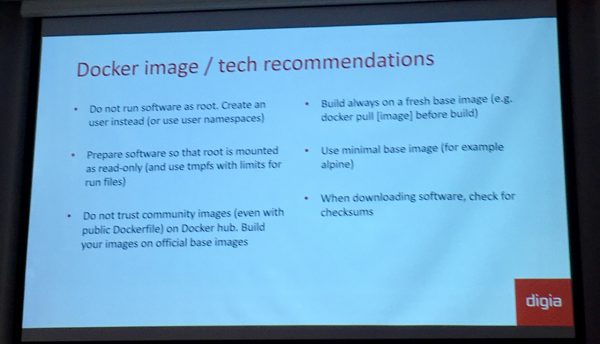
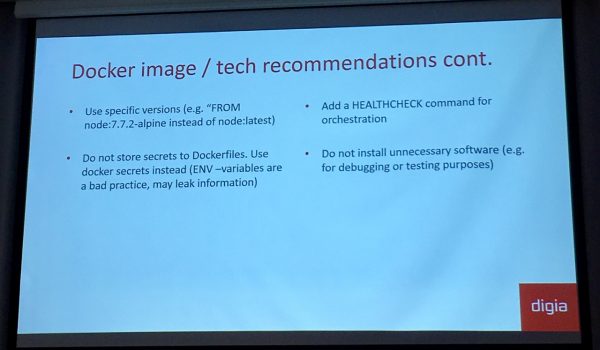
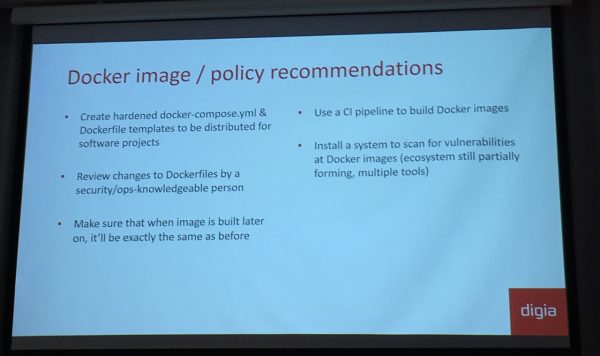
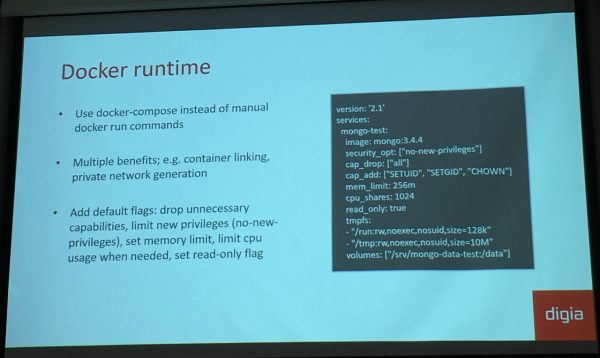
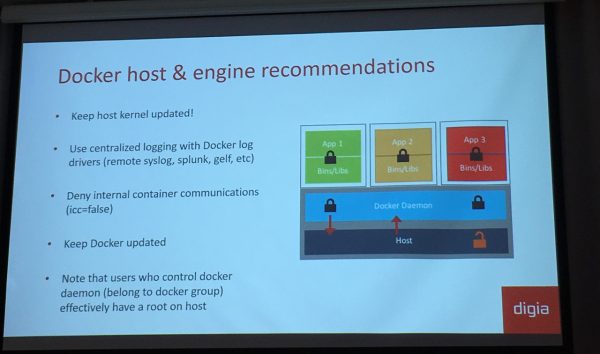
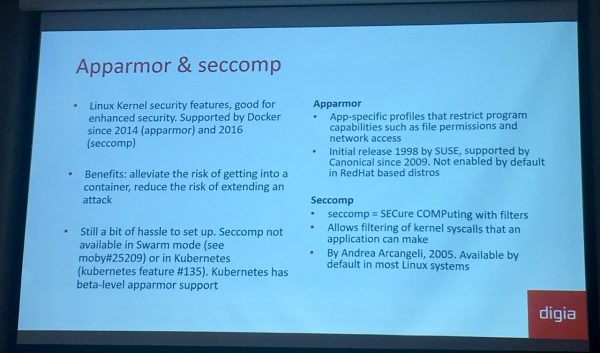
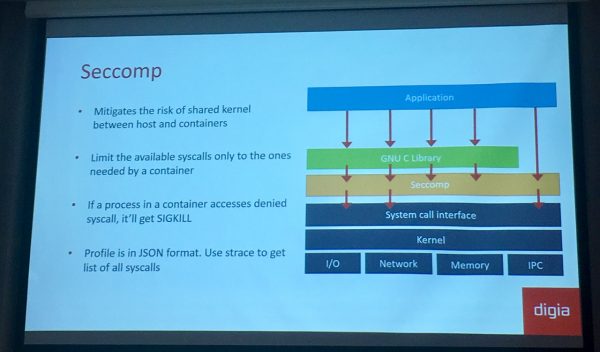
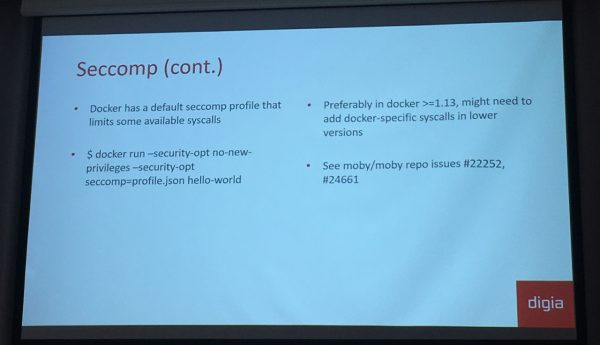
Docker Security
Docker is currently experiencing very high adoption rate and people are deploying on Docker without considering the security landscape. Mika Vatanen from Digia told us about Docker Security (slides, pdf), possible attack vectors, how Docker handles security and what recommendations we should use when using it.
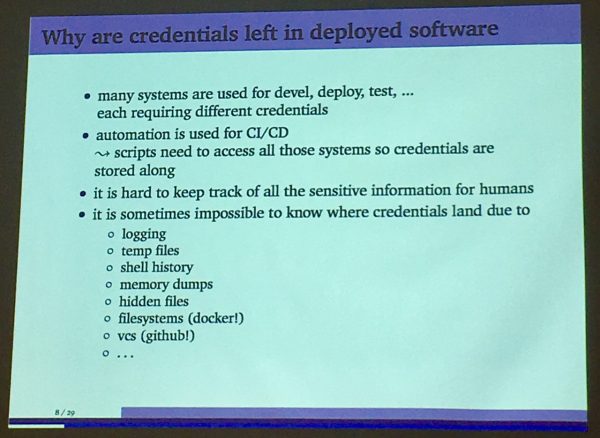
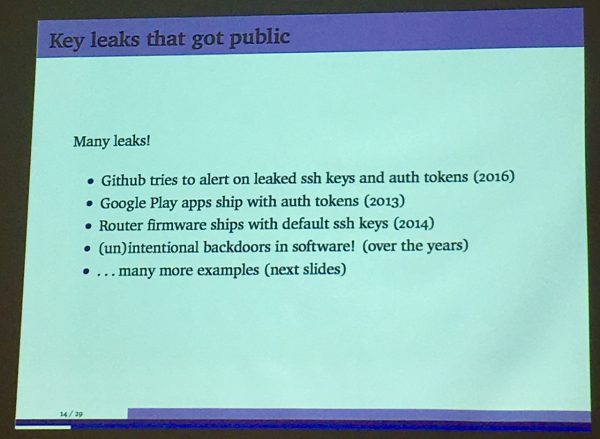
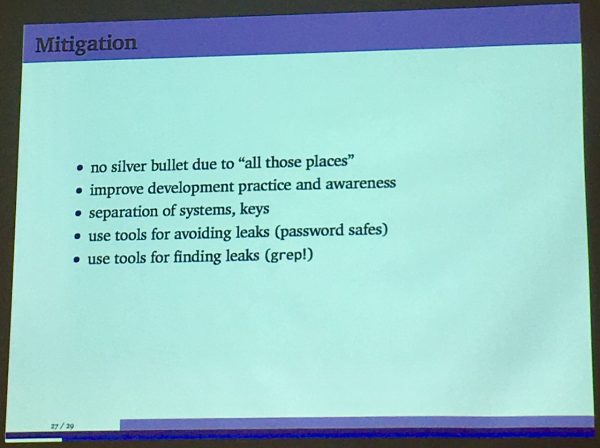
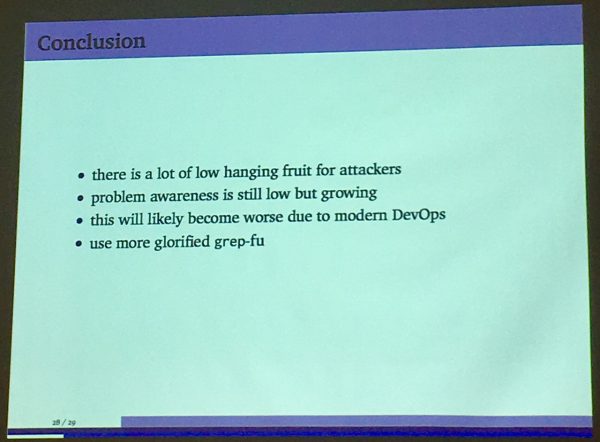
Leaking credentials – a security malpractice more common than expected
Bogdan Mihaila from Synopsys talked about Protecode and research of leaked credentials (slides, pdf).
Upcoming: DevSecOps “mini-hackathon”
Last topic was introduction to upcoming “mini-hackathon” by Pekka Sillanpää from OWASP Helsinki. They are planning a hands-on event in August for familiarizing and investigating some nice open source tools, including: OWASP Dependency-Check, ZAP Proxy, OWASP DefectDojo, DevSec hardening framework and Clair. See more info from OWASP Helsinki page.
Leave a Reply