Category: Tech
-
Raspberry Pi 3+ and Joy-IT 7″ touchscreen on Debian 11
I’ve had for sometime a Joy-IT 7″ IPS display for Raspberry Pi waiting in my drawer and now I got around to put it into use with Ikea Ribba frame. Setting up the touch screen was easy but getting it inverted (upside down) took some extra steps. The touchscreen is “RB-LCD-7-2″ from Joy-IT which is…
-
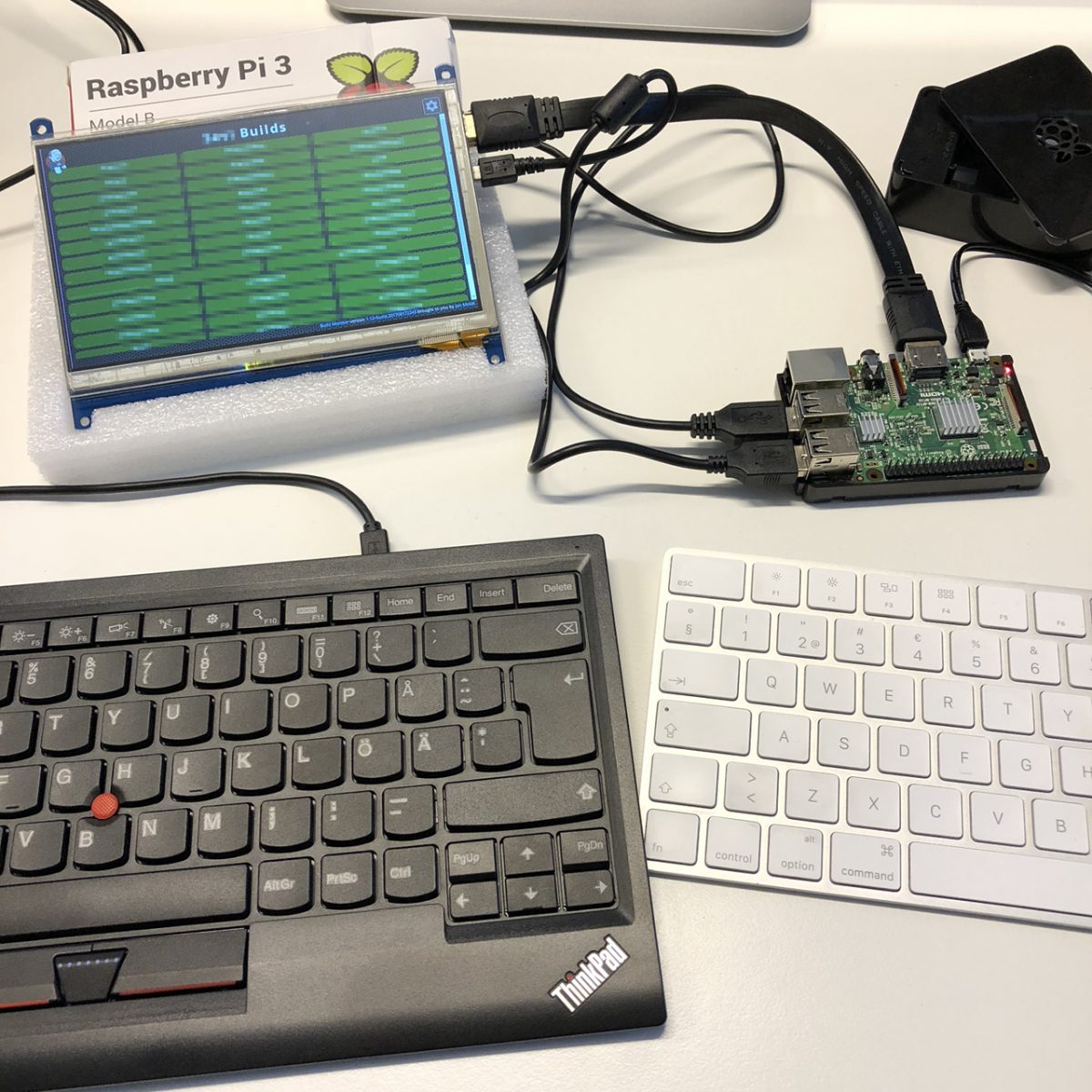
Build Monitor with Raspberry Pi and Touch Screen
Information is a great tool in software development and it’s useful to have easy access to it. The more obvious you make your problems, the harder you make them to ignore. The more attention they get, the quicker they get solved. One thing developers like to monitor in software development is continuous integration status and…
-
Using Apache for proxying connections to Crucible
Atlassian’s web applications are great tools for software development and they are relatively easy to setup because they come with Jetty servlet container and HQSQL database. You only have to install Java. Some of the applications can be also run like any normal deployable WAR-packaged web application for example with Apache Tomcat which gives you…
-
Running FishEye & Crucible as a service in Linux
Atlassian’s tools for supporting software development are great but they aren’t really admin friendly to start with. For example FishEye & Crucible doesn’t ship with scripts to start it at system boot time but with the help of Atlassian’s Wiki, sysadmin tasks and scripts you can run it as a normal service.… Jatka lukemista →
-
Using CAcert.org signed certificates for TLS
Setting up Transport Layer Security (TLS), or as previously known as Secure Sockets Layer (SSL), for Apache, Postfix and IMAP like Dovecot is fairly easy. You just need some digital certificates and configuration. If you don’t want to pay for certificates from trusted sources like Thawte or you just don’t need that kind of trust…
-
Installing Apache Tomcat 6 on CentOS
CentOS is great substitute for Red Hat Enterprise Linux but is missing some useful packages like Apache Tomcat 6. Installing Apache Tomcat 6 on CentOS 5 from gzip-package is fairly easy. The following guide is at least for CentOS 5.4. Pre-Requirements First you need to install Sun JDK and you can follow the instructions given…
-
Installing Sun JDK 1.6 on CentOS
CentOS doesn’t have a package for Sun JDK so it has to installed manually. It’s fairly easy but there are some steps to do that. This guide has been tested on CentOS 5.4 x64_86. Step 1. Initial setup for building RPM -!- Do this with a non-root user Create ~/.rpmmacros $ vim ~/.rpmmacros… Jatka lukemista…
-
Redirect HTTP and HTTPS traffic to Tomcat’s ports
Apache Tomcat likes with default settings to listen to requests on 8080 and 8443 ports but it is more enjoyable to use the more common 80 and 443 ports for HTTP and HTTPS traffic. This way the user don’t have to put those pesky port numbers after the address. Of course you could just tell…
-
Keeping up with the time in Xen
A simple tip for keeping up with the time in Xen when your domU isn’t syncing the clock frequently enough and your clock is whatever. Of course you can sync your clock with ntpdate but first you need to set the domain (domU) to run its wallclock independently from Xen. Simply say in the command…
-
Samba performance problem after kernel update
Samba is a nice service to provide storage space through networks and it is relatively easy to set up. It’s not as fast as using NFS between Linux hosts but sometimes you don’t have that possibility. Sometimes there also might be quite confusing problems like I happened to notice. My Samba service had worked fine…