Year: 2020
-
Short notes on tech 52/2020
Week 52, 2020 Code TIL you can get the git log of a *specific function* in a file. 🤯 Where was this all my life? git log -L:<function>:filehttps://t.co/HpVcLS8Yhc pic.twitter.com/5MqbciqjoF— Todd Gamblin / @tgamblin@hachyderm.io (@tgamblin) December 21, 2020 Learning Stop using Material Design text fields!“But Google uses it!” — yeah, that’s not a good enough reason.……
-
Short notes on tech 51/2020
Week 51, 2020 Cloud AWS launches new managed services: Announcing Amazon Managed Service for Grafana (in Preview) and Amazon Managed Service for Prometheus. Monitoring & securing AWS with Microsoft“Interesting approach, how to setup (advanced) monitoring of AWS with Azure Security Center (CSPM), Azure Defender (CWPP), Cloud App Security (CASB), and Azure Sentinel (SIEM).”… Jatka lukemista…
-
Short notes on tech 50/2020
Week 50, 2020 Cloud Wait, Docker is deprecated in Kubernetes now? What do I do?tl;dr; Use CRI runtimes instead: containerd or CRI-O. Google Cloud: default container runtime to change to Containerd with GKE node version 1.19 and higher.“As the Docker container runtime will be removed from the Kubernetes project in the future, GKE is beginning…
-
Short notes on tech 49/2020
Week 49, 2020 Development and Operations Using SSL certificates from Let’s Encrypt in your Kubernetes Ingress via cert-managerWalkthrough of the process of automating the issuance and renewal of certificates provided by Let’s Encrypt for Kubernetes Ingress using the cert-manager add-on. (from cloudseclist.com) Use Amazon EC2 Mac Instances to Build & Test macOS, iOS, ipadOS, tvOS,…
-
Short notes on tech 48/2020
Week 48, 2020 Tools of the Trade Next.js 10Built-in Image Component and Automatic Image Optimization, Internationalized Routing, Next.js Analytics, React 17 Support. Node.js 15Throw on unhandled rejections, pm 7 includes yarn.lock file support, peer dependencies are now installed by default, V8 8.6. kachkaev/njt“njt (npm jump to): a quick navigation tool for npm packages”.… Jatka lukemista…
-
Monthly notes 54
Working from home continues as COVID-19 still surges and if you yet haven’t checked your video call capabilities, read the How to make video calls almost as good as face-to-face article. The remote working isn’t going away as this year has shown that pendeling to offices every day isn’t really needed.… Jatka lukemista →
-

Prettifying AWS S3 Bucket public index list
Sometimes it’s useful to have a index listing on a AWS S3 bucket. Here are some solutions to configure it with nice template. If having a public index list on a S3 Bucket is a good idea or not I’m not saying yay or nay. First set the correct Bucket Policy { “Version”: “2012-10-17”, “Statement”:…
-

What software and hardware I use
There was a discussion in Koodiklinikka Slack about what software people use and that people have made “/uses” pages for that purpose. And inspired by Wes Bos /uses from “Syntax” Podcast here’s my list. Check my /uses page to see what software and hardware I use for full-stack development in JavaScript, Node.js,… Jatka lukemista →
-
Monthly Notes 52
Issue 52, 9.9.2020 Software development Field Ops Guide“The Field Ops Guide (by Futurice) is a booklet that makes it possible to survive a software development project. It’s a distillation of years of wisdom gathered working in client projects.” Kubernetes Threat matrix for Kubernetes“While Kubernetes has many advantages, it also brings new security challenges that should…
-
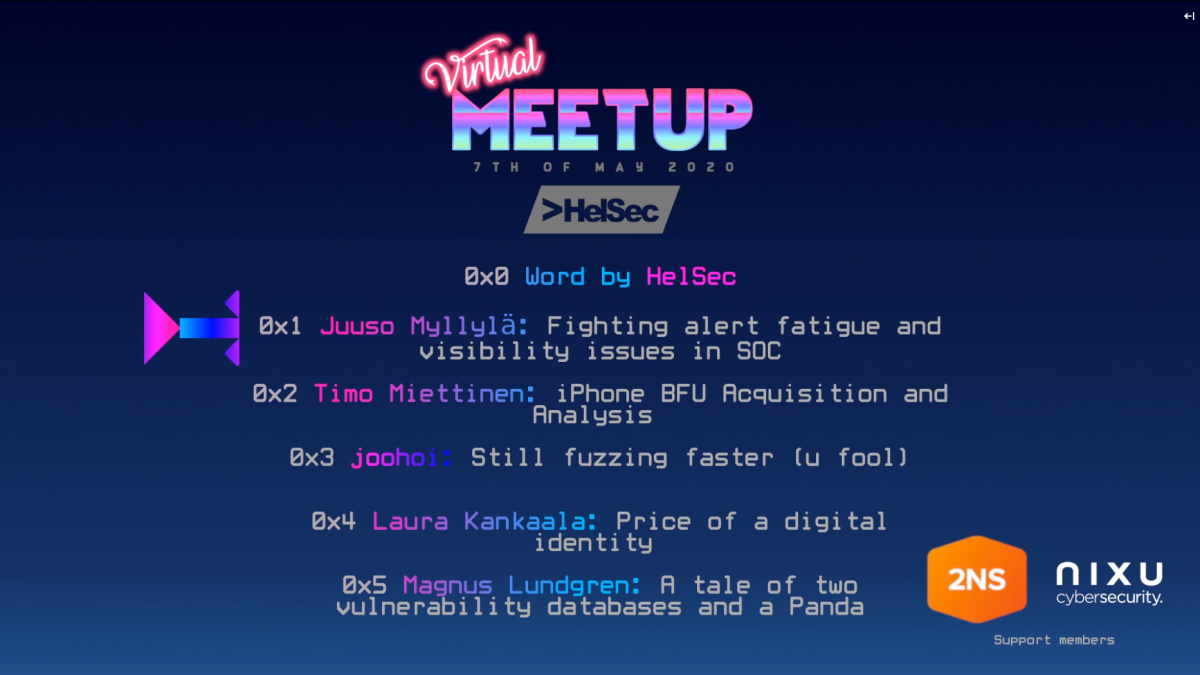
Notes from HelSec Virtual Meetup 1
This year has been challenging for meetups and gatherings but one good side of the restrictions was that remote work has become more acceptable and also meetups and conferences have invested to streaming and virtual participation which is great for people living in an area where there’s no meetups. In early May HelSec kept their…